The History and Evolution of the ISO 27000 Series: How the World’s Leading Information Security Standards Developed
Information security did not begin with ISO 27001, and the ISO 27000 series did not appear all at once. What many organizations now take for granted as the leading international framework for
managing information security was built gradually, over decades, in response to real business needs, rising digital dependence, and a growing awareness that information risk could no longer be managed in an informal way.
Today, the ISO 27000 series provides a broad and structured body of standards for building, operating, improving, and assessing an Information Security Management System, or ISMS. At the center of the series stands ISO/IEC 27001, the requirements standard against which organizations can be certified. Around it sits a broader ecosystem of related standards covering controls, implementation, risk management, measurement, auditing, governance, sector specific needs, cloud security, and privacy. ISO/IEC 27000 itself describes this as an ISMS series of standards that includes requirements standards, support and guidance standards, sector specific guidance, and standards related to conformity assessment.
Understanding how we got here helps explain why the standards are structured the way they are today. It also helps explain why the series continues to evolve. The history of the ISO 27000 series is really the history of information security becoming a management discipline, not just a technical concern.
Why Information Security Needed Standards in the First Place
Before formal information security standards existed, organizations still tried to protect information, but they did so in fragmented and inconsistent ways. Security was often driven by local habits, individual experts, or isolated technical measures. One company might rely heavily on physical controls and policy manuals, another on informal trust and technical tools, and another on a patchwork of contractual or regulatory requirements. There was no single, widely accepted framework that organizations across sectors and countries could follow.
That became a serious problem as digital transformation accelerated. Information was no longer just stored in filing cabinets and archive rooms. It began to flow through corporate networks, shared systems, databases, remote connections, early internet facing services, and increasingly interconnected supply chains. As dependence on digital information grew, so did the consequences of poor security. Loss of confidentiality, corruption of data, downtime, fraud, operational disruption, and reputational harm all became far more visible and far more expensive.
Organizations needed more than technical fixes. They needed shared concepts, common terminology, consistent expectations, and a structured way to manage security over time. They needed something that leadership could understand, auditors could assess, and business partners could trust. This is the problem that eventually gave rise to the standards we now know as the ISO 27000 series.
The British Origins, How BS 7799 Laid the Groundwork
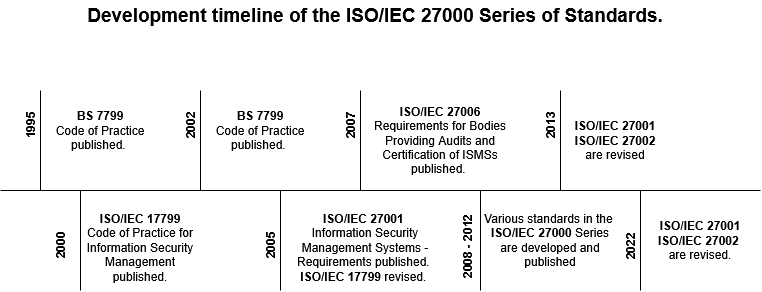
The story begins in the United Kingdom. In 1995, the British Standards Institution, or BSI, published BS 7799, an important early milestone in the development of formal information security standards. BS 7799 was not yet the global standard people recognize today, but it was a major step forward because it moved information security out of the realm of scattered good intentions and into a more structured standardization effort.
BS 7799 is especially important because it introduced two ideas that would shape the future of the series. First, it recognized that organizations benefit from a code of practice containing structured information security controls. Second, it helped move the conversation toward something bigger than a list of controls, namely the management system concept.
That second point matters greatly. A control list can tell an organization which practices may be useful, but a management system forces the organization to think more broadly. It requires attention to policy, responsibilities, planning, scope, risk, monitoring, review, and continual improvement. In other words, it shifts information security from being a technical checklist into an organizational discipline.
From a historical point of view, that is one of the most important reasons the later ISO standards became so influential. They did not simply tell organizations to install controls. They required organizations to manage information security systematically.
How ISO and IEC Became Involved in Information Security Standardization
As information risks became more international, a national standard was no longer enough. Global business needed a global framework. Organizations operating across borders needed standards that customers, regulators, suppliers, and certification bodies could all recognize. This is where ISO and IEC became central.
ISO, the International Organization for Standardization, is a worldwide federation of national standards bodies. IEC, the International Electrotechnical Commission, works closely with ISO on electrotechnical standardization. In the information security area, the work is carried out through ISO/IEC JTC 1, SC 27, the joint technical structure responsible for these standards. ISO/IEC 27000 explains that ISO/IEC JTC 1/SC 27 maintains the expert committee dedicated to the development of the ISMS series of standards.
This international governance structure is one reason the series gained such credibility. These were not the private rules of one vendor or one country. They were developed through international standardization processes and maintained as part of a formal global system.
That broader framework also helped information security standards become part of a wider management system culture. ISO had already established strong credibility through standards in areas such as quality and environmental management. When information security matured into a management issue, ISO was a natural institutional home for it.
The Transition from BS 7799 to ISO/IEC 17799
The first major step toward internationalization came when the code of practice part of the British work was adopted internationally. BS 7799 Part 1 became ISO/IEC 17799 in 2000. This was a pivotal development because it showed that the security guidance first articulated in the UK had broader international relevance.
This stage is important because it established the control guidance tradition that later evolved into ISO/IEC 27002. It confirmed that organizations needed not just general statements about security, but a practical body of control guidance that could be referred to during implementation.
At this point, however, the management system side of the story was still developing. A code of practice is useful, but it is not enough on its own to support certification against a full management system model. The next step would change that.
The Birth of ISO/IEC 27001 in 2005
In 2005, the first international version of ISO/IEC 27001 was published. This was the moment at which the modern ISMS framework truly took shape. ISO/IEC 27001:2005 gave organizations a formal requirements standard for establishing, implementing, operating, monitoring, reviewing, maintaining, and improving an Information Security Management System.
This changed the conversation in several ways.
First, information security could now be managed within a recognized management system framework, rather than through isolated technical controls or local practices.
Second, organizations now had a certifiable standard. This was a major practical advantage. It meant they could demonstrate conformity through external audit, helping to build confidence with customers, regulators, business partners, and procurement teams.
Third, ISO/IEC 27001 established risk management as central to information security governance. Controls were no longer chosen merely because they seemed sensible or fashionable. They were to be selected in light of the organization’s context, risks, treatment decisions, and management objectives.
That basic logic still defines the standard today. The current ISO/IEC 27001:2022 states that the document specifies requirements for establishing, implementing, maintaining, and continually improving an information security management system, and that it includes requirements for the assessment and treatment of information security risks tailored to the organization’s needs. It also makes clear that the requirements are generic and intended to be applicable to organizations of all types, sizes, and sectors.
Why the Management System Concept Was So Important
To understand why ISO/IEC 27001 became so influential, it is necessary to understand the management system idea behind it. The standard did not become popular simply because it listed useful controls. Its real strength was that it gave organizations a structure for governing information security as a repeatable and improvable process.
ISO/IEC 27000 explains that international standards for management systems provide a model for setting up and operating a management system, reflecting the international state of the art as reached by experts in the field. It also explains that organizations can use the ISMS series to develop and implement a framework for managing the security of information assets, including financial information, intellectual property, employee data, and information entrusted by customers or third parties.
ISO/IEC 27003, which supports implementation of ISO/IEC 27001, reinforces this idea. It explains that an ISMS emphasizes understanding organizational needs, establishing policy and objectives, assessing information security risks, implementing and operating controls and processes, monitoring and reviewing performance, and practising continual improvement. It further notes that an ISMS includes policy, assigned responsibilities, management processes, documented information, risk assessment, and risk treatment.
This is the real heart of the series. Information security is not treated as a one time project. It is treated as a management discipline that must be governed, resourced, reviewed, and improved.
The 2013 Revision, A More Mature and Integrated Standard
The next major turning point came in 2013. ISO/IEC 27001:2013 was a major revision that brought the standard into closer alignment with the wider world of ISO management system standards. This alignment mattered for organizations that were already operating quality, environmental, or service management systems, because it made integration easier and more natural.
The current 2022 edition of ISO/IEC 27001 notes that it applies the high level structure and common management system approach defined in Annex SL, which supports compatibility with other management system standards. The 2013 revision was the crucial stage in that broader integration journey.
In practical terms, the 2013 version placed stronger emphasis on organizational context, interested parties, leadership, documented information, performance evaluation, and continual improvement. It also helped organizations move away from a narrow view of security as an IT issue. Information security became more clearly embedded within organizational governance and risk management.
This shift is reflected in ISO/IEC 27003 as well. That document emphasizes that top management must ensure responsibilities and authorities relevant to information security are assigned and communicated, and that leadership is essential for ensuring that the ISMS conforms to requirements and performs effectively.
The 2013 revision therefore did not merely update wording. It represented a maturing understanding of how information security needs to function inside real organizations.
The 2022 Revision, Modernizing the Standard for a Changed World
The 2022 revision continued this development. It did not discard the management system philosophy, but it updated the standard to remain relevant in a very different security environment. By 2022, organizations were dealing with much more than traditional office networks and on premises infrastructure. They were managing cloud services, remote and hybrid working, outsourced development, SaaS dependency, more complex supplier ecosystems, and a threat landscape shaped by ransomware, modern cybercrime, and fast moving technical change.
The 2022 foreword to ISO/IEC 27001 notes that the document was revised to align with the harmonized structure for management system standards and with ISO/IEC 27002:2022. The standard continues to place strong focus on leadership, planning, risk, and continual improvement. For example, Clause 6 requires the organization to determine risks and opportunities, address them through planned actions, integrate those actions into ISMS processes, and evaluate their effectiveness.
This modernized structure matters because information security is no longer a static field. Organizations need standards that remain applicable in a changing technological environment. The 2022 revision helped ensure that ISO/IEC 27001 remained relevant without abandoning the core management principles that made it successful in the first place.
How ISO/IEC 27002 Evolved Alongside ISO/IEC 27001
No discussion of the history of the ISO 27000 series is complete without ISO/IEC 27002. Historically, ISO/IEC 27002 grew out of the code of practice lineage that began with BS 7799 Part 1 and then became ISO/IEC 17799. It later evolved into the standard now known as ISO/IEC 27002, which serves as the principal guidance document for information security controls.
Its role is different from that of ISO/IEC 27001. ISO/IEC 27001 is the requirements standard. It tells organizations what they need in order to claim conformity to the ISMS requirements. ISO/IEC 27002, by contrast, provides a reference set of generic information security controls and implementation guidance. The 2022 edition explicitly states that it is designed for organizations using ISO/IEC 27001, implementing internationally recognized good practices, or developing organization specific guidelines.
This relationship is one of the defining features of the series. ISO/IEC 27001 tells you what must be addressed at the management system level. ISO/IEC 27002 helps explain control guidance that may support risk treatment decisions inside that system.
The 2022 revision of ISO/IEC 27002 was especially significant because it reorganized the controls into four themes, organizational, people, physical, and technological, and introduced attributes that allow organizations to view controls through different lenses. The document shows how controls can be categorized using attributes such as control type, information security properties, cybersecurity concepts, operational capabilities, and security domains.
This was not a cosmetic change. It reflected a more flexible and modern way of working with controls, one better suited to current operational realities.
How the Wider ISO 27000 Series Expanded
As ISO/IEC 27001 and ISO/IEC 27002 became established, the series naturally expanded. Organizations needed more than a requirements standard and control guidance. They needed vocabulary, implementation support, risk guidance, audit support, sector specific advice, governance frameworks, and specialized standards for cloud and privacy.
ISO/IEC 27000 plays a crucial role here because it maps the series and explains its structure. It presents the ISMS series as an organized body of standards, not a random collection of publications.
Some of the most important standards in the broader series include ISO/IEC 27003, which provides guidance for the successful implementation of an ISMS in accordance with ISO/IEC 27001. ISO/IEC 27000 describes it precisely in those terms.
Then there is ISO/IEC 27004, which addresses monitoring, measurement, analysis, and evaluation, helping organizations assess information security performance and the effectiveness of the ISMS.
ISO/IEC 27005 focuses on information security risk management and supports the general concepts specified in ISO/IEC 27001. It helps organizations implement a process oriented approach to risk.
ISO/IEC 27007 supports ISMS auditing, while ISO/IEC TR 27008 provides guidance for auditors reviewing information security controls.
ISO/IEC 27013 supports integrated implementation with ISO/IEC 20000 1, showing how security management can be aligned with service management. ISO/IEC 27014 addresses governance of information security, recognizing that governing bodies increasingly need visibility and oversight in this area.
The series also expanded into sector specific and domain specific guidance. ISO/IEC 27002 points readers toward additional standards such as ISO/IEC 27017 for cloud services, ISO/IEC 27701 for privacy, ISO/IEC 27019 for energy, ISO/IEC 27011 for telecommunications, and ISO 27799 for health.
This is one of the clearest signs of how mature the series has become. What began as a foundational approach to information security management has developed into a broad framework capable of supporting diverse industries and use cases.
Why the ISO 27000 Series Became the Global Reference Point
The ISO 27000 series became globally influential because it addressed several problems at once.
It gave organizations a common language for discussing information security.
It provided a structured framework for managing information security systematically rather than reactively.
It supported certification and external assurance.
It allowed flexibility, because the standards are generic and applicable to organizations of different sizes, sectors, and risk profiles.
And it linked information security to leadership, governance, and continual improvement.
ISO/IEC 27000 itself describes the benefits of the ISMS series in practical terms. These include a structured framework, assistance for management, promotion of globally accepted good practices in a non prescriptive form, a common conceptual basis for information security, and increased stakeholder trust.
That combination is powerful. The standards are structured enough to create confidence, but flexible enough to be used by different organizations in different contexts. This balance is one of the main reasons ISO/IEC 27001 certification became so important in procurement, customer assurance, and regulatory discussions.
Conclusion, From No Common Standard to a Global ISMS Series
The history of the ISO 27000 series is the story of information security becoming organized, standardized, and internationally governed. It began in a world where security practices were often inconsistent and local. It took shape through early British standardization work. It expanded internationally through ISO and IEC. It matured into a certifiable management system with ISO/IEC 27001. And it evolved into a broad and sophisticated series that now supports implementation, measurement, risk management, auditing, governance, cloud security, privacy, and sector specific application.
That history still matters. It explains why ISO/IEC 27001 is more than a control checklist, why ISO/IEC 27002 remains so important, and why the wider series continues to grow. The standards were not created simply to document good ideas. They were developed to help organizations manage information security in a disciplined, risk aware, and continually improving way.
In that sense, the ISO 27000 series did not just respond to the rise of digital risk. It helped define how modern organizations think about information security itself.